The Office of Information Security has observed a trend in which criminals advertise a job while impersonating someone from a university in Mexico. Impersonation is one of the most effective social engineering tactics scammers use, and it can be particularly enticing if offered employment. If you see a message like the one below, please do […]
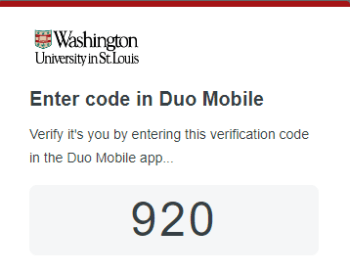
Scam of the Month: Washington University – internship and management Programs – PAID












![From: Wustl Health Care Center Subject: Emergency Notice: COVID-19 Variant Poses Risks in our University I trust this message finds you in good health. I am writing to share critical information that impacts the health and safety of our academic community. Regrettably, we have recently received confirmation of a positive COVID-19 variant test result for a member of our university staff. Despite a significant portion of our staff and faculty being vaccinated, it is crucial to acknowledge that certain variants may pose challenges even to those who have received the vaccine. As a precautionary measure, we are actively initiating contact tracing to identify and mitigate potential risks. To assist us in determining whether you have been in close proximity to the affected staff member, we have established a dedicated webpage for your convenience. Please click the following link: [Access Detailed Staff Information] to review specific details about the individual in question. Prompt reporting of any interactions or contact is crucial, as it greatly contributes to the overall safety and security of our community. We understand that this news may be concerning, but please rest assured that our medical team is available to address any questions and provide guidance. You can contact them at [Healthcare@wustl.edu], and they will offer the necessary assistance. Our commitment to your well-being and the creation of a secure working environment remains steadfast. We kindly ask for your cooperation in this matter, as it is vital for our collective efforts to contain the virus and uphold the safety of our community. Confidentiality Notice: This email and its attachments are confidential and intended solely for the recipient. In line with privacy guidelines, we kindly request that you refrain from sharing or forwarding this message. PLEASE AVOID SHARING THIS EMAIL WITH ANYONE. We sincerely appreciate your dedication to our university community, and together, we will navigate through this challenge and emerge stronger. Best regards, Washington University in St. Louis Health Care Center Contact: (616) 526-7052](https://informationsecurity.wustl.edu/files/2024/01/scam_covid-ae533c8153fb28b6-350x130.png)