The Office of Information Security has identified a trend in which criminals send members of our community account termination emails containing a malicious link. They hope a victim will give their WashU credentials in a Google Form. In this scam, hackers use a legitimate WashU email address to send phishing emails. Victims who click the phishing link are taken to a Google Form and asked to enter their WUSTL Key and password.
If you see a message like the one below, please do not interact with the sender and do not follow any special instructions. Simply report the email using the Phish Alert Button (PAB) in your Outlook interface. It is always best to be cautious and report anything remotely suspicious. Our team will analyze all submissions and return them to you if they are determined to be safe. Below, we dissect this phishing attempt to reveal its red flags.
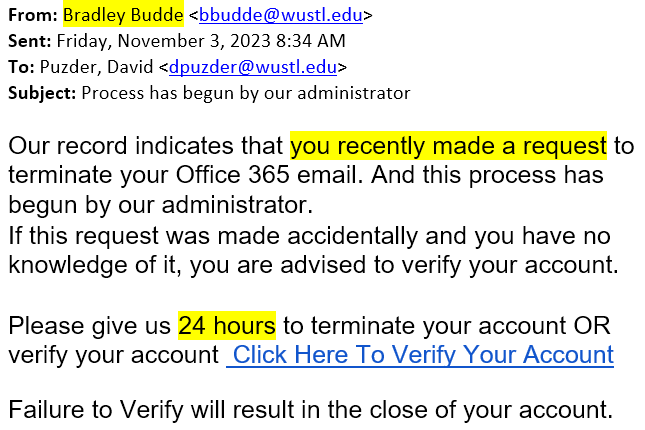
- The sender is from WashU, but they work in Neurology. This email address has no business sending account termination emails.
- “Process has begun by our administrator” is suspiciously vague. It could apply to any organization.
- It claims I recently requested to delete my account. This must be a mistake, so I should call the service desk at 314-933-3333.
- A 24-hour time limit pressures me into making hasty decisions.
- If I hover my mouse over the link, the preview shows a link to Google Forms. Lately, hackers have used Google Forms to steal our credentials. You should never enter your credentials into a Google Form.
- There are spelling and grammar errors throughout.
Avoid this and other scams by following our ten phishing safety tips and related guidance below.
10 Phishing Safety Tips
- Don’t click. Instead of clicking on any link in a suspicious email, type in the URL or search wustl.edu for the relevant department or page. Even if a website and/or URL in an email looks real, criminals can mask its true destination.
- Be skeptical of urgent requests. Phishing messages often make urgent requests or demands. When you detect a tone of urgency, slow down and verify the authenticity of the sender and the request by using official channels rather than the information provided by the sender.
- Watch out for grammar, punctuation, and spelling mistakes. Phishing messages are often poorly written. Common hallmarks of phishing are incorrect spelling, improper punctuation, and poor grammar. If you receive an email with these problems, it may be a phishing attempt. Double-check the email address of the sender, don’t follow any links, and verify the authenticity of the request using official channels.
- Keep your information private. Never give out your passwords, credit card information, Social Security number, or other private information through email.
- Pick up the phone. If you have any reason to think that a department or organization really needs to hear from you, call them to verify any request for personal or sensitive information. Emails that say “urgent!”, use pressure tactics, or prey on fear are especially suspect. Do an online search for a contact phone number or use the contact number published in the WUSTL directory.
- Use secure websites and pay attention to security prompts. Always check if you are on a secure website before giving out private information. You can determine whether a website is secure by looking for the “https:” rather than just “http:” in the Web address bar or for the small lock icon in the Internet browser. If your browser cannot validate the authenticity of the website’s security certificate, you will be prompted. This is frequently a telltale sign of fraud, and it would be a good time to pick up the phone or report a suspicious message.
- Keep track of your data. Regularly log onto your online accounts and make sure that all your transactions are legitimate.
- Reset any account passwords that may have been compromised.
- Know what’s happening. Visit the Office of Information Security Alerts page often.
- Report it. If you are a victim of an email scam, report it to our office by using the Phish Alert Button (PAB). When you report a phishing attack, we will investigate it and, if necessary, remove other instances of the attack from our systems. Reporting the attack will help protect others and our institution.
Additional Resources
Phishing | Office of Information Security | Washington University in St. Louis
Phishing 101 | Office of Information Security | Washington University in St. Louis