Attackers continuously adjust their tactics to circumvent our defensive strategies, using new methods to access our systems, data, and personal information. Even as attackers develop new scams, one element seems to carry on—impersonation. Our office frequently publishes about impersonation because it forms the basis of most phishing attempts.
Often, attackers impersonate a high-ranking employee in an organization. They use a tone of urgency and threaten consequences if the recipient fails to act quickly. We should remain vigilant about these high-level impersonation attacks.
As expected, some attackers are aware that the word is out about high-level impersonation. They have adjusted their strategy by impersonating people who are not high-ranking within the organization.
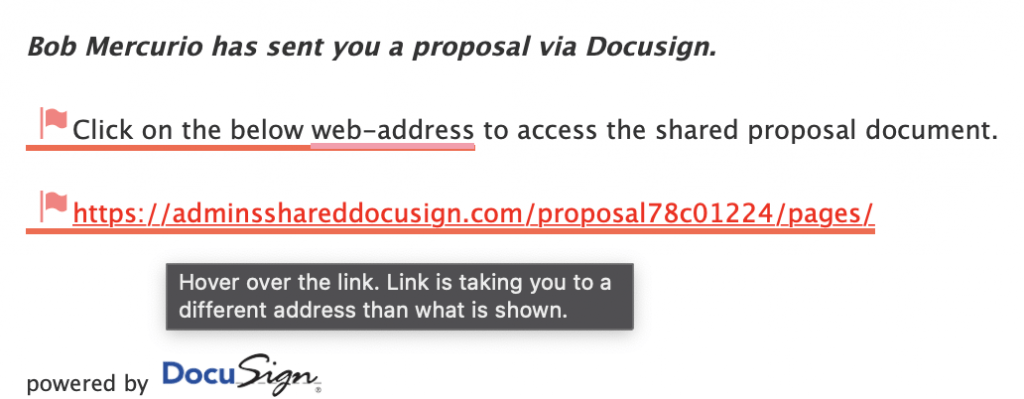
Some of these attackers have impersonated employees requesting DocuSign signatures to fool their victims into revealing sensitive information such as logins and passwords. These malicious emails urge users to sign in to view a DocuSign request. Legitimate emails from DocuSign do NOT ask users to sign in. Instead, they use an authentication code that is sent directly to the recipient. Please be on the lookout for these malicious emails that hope to take advantage of DocuSign users.
As always, please be vigilant when checking emails, particularly if they are from unknown sources.